· 3 min read
The Many Methods of Managing Customers and Multi-tenancy
- The service is expected to be delivered "as-a-Service" - Customers have many different risk profiles - It's difficult to explain how commercials affect risk - It can feel like you're **custom-building solutions for eve.

Being an MSP Today Is Complicated
- The service is expected to be delivered “as-a-Service”
- Customers have many different risk profiles
- It’s difficult to explain how commercials affect risk
- It can feel like you’re custom-building solutions for every customer
This Blog Post Will Give You Tools to Help Your Customers Understand:
- How risk, economics, and performance interact
- Why Multi-tenancy might or might not be right
- Where they can use Multi-tenancy internally to manage costs
We’ll explore common customer scenarios and the drivers that justify Multi-tenancy—framed in a way that helps your customers understand your value.
Future blog posts in this series will cover:
- The economics of MSP services – deep dive into Multi-tenancy
- When is single tenant right for my customer and business?
- Navigating cloud: Office 365, Citrix Cloud, and others
- Solution deep-dives by customer type
🏗️ Building a Multi-Tenant AD
When does it work? When is it still relevant?
Scenario 1 – The ISV-Focused App
The Situation
You offer a specific line-of-business app that many of your customers use. Common examples:
- QuickBooks (older versions)
- Healthcare apps for clinics or vets
- Legal platforms
- Country/region-specific ERPs
You’re not hosting full environments—just the app, often via Citrix XenApp or RDS.
Why Multi-Tenancy Works Here
- The app is stable and unchanging
- No cloud version available or not mature
- Switching costs are high
- No real alternative exists
This makes multi-tenant AD hosting ideal. It allows:
- Easier security control
- Fast onboarding via automation tools like Atria
- Shared SQL, allowing investments in high availability
- Cost-efficient scaling
Scenario 2 – The Small Customer
Most of your targets are <50 users, sometimes up to 500. These customers are:
- Easier to win
- Simpler to manage
- Often want full-stack IT from one provider
- Likely running legacy systems (even Windows XP 😬)
- Want remote access (especially post-COVID)
- Want to avoid CapEx and favor operational flexibility
Multi-tenancy helps:
- Deliver modern, secure desktops at low cost
- Support remote and hybrid work
- Leverage cloud tools like Office 365, Azure, AWS
- Provide a flexible path to full cloud adoption
Scenario 3 – The Conglomerate / Government
You’re supporting a government agency or business conglomerate with:
- Multiple departments or companies
- Each wanting some control but sharing broad IT goals
- Separate infrastructures or Office 365 tenants
- Security and compliance requirements
Why Multi-Tenancy Still Makes Sense
While it may seem counterintuitive, multi-tenancy works here because:
- Security/commercial goals are shared
- You’re building an isolated, shared environment
- It becomes an economic discussion, not just a technical one
Benefits:
- Shared infrastructure = lower cost
- Central helpdesk
- Single deployment = faster provisioning
- Automation becomes scalable (via Atria or custom scripts)
- Training, support, and ops standardization across departments
Dedicated apps, file servers, or SQL can still be isolated as needed
But AD remains unified for manageability and scale
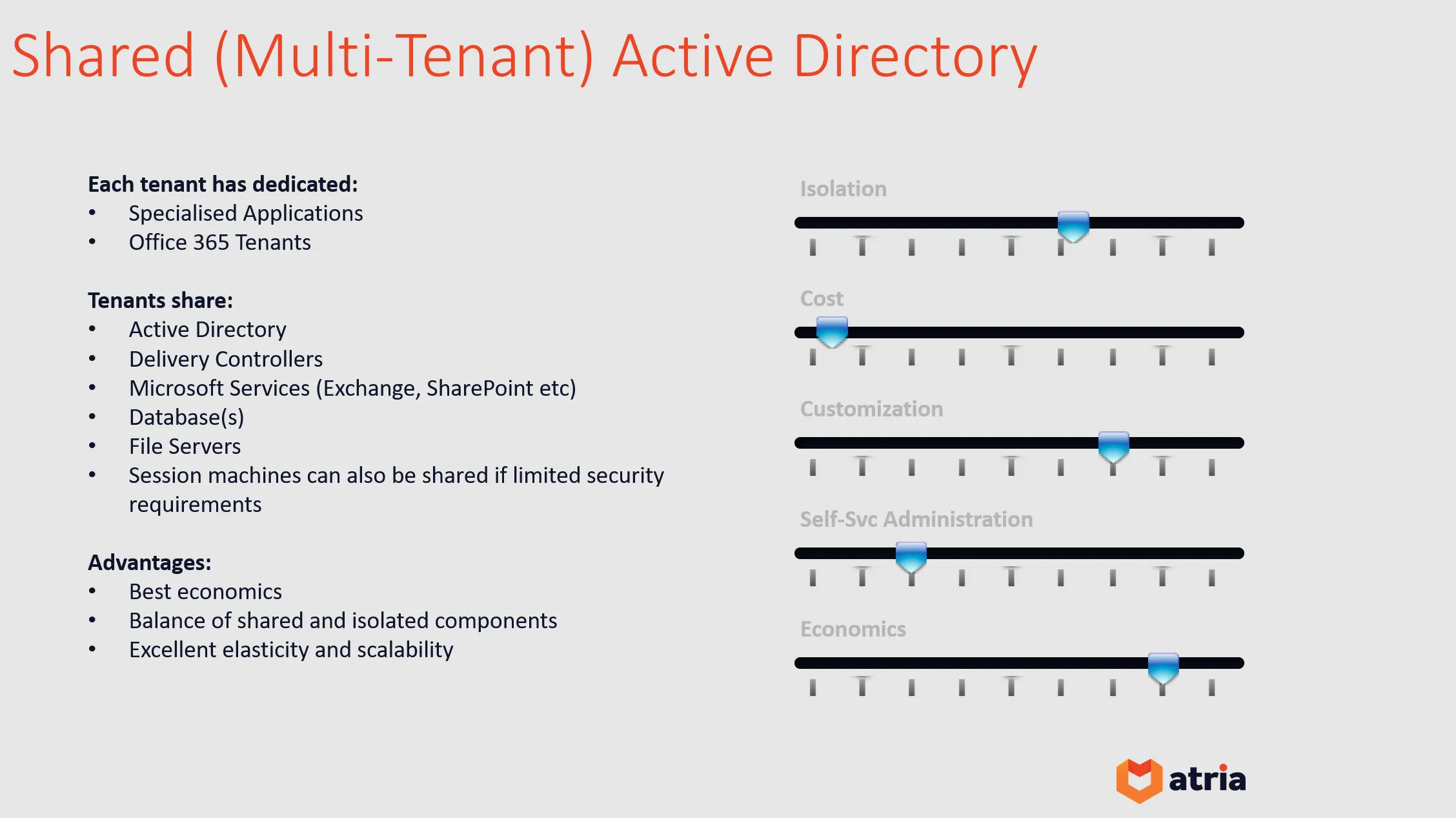
🧠 Multi-Tenant Summary
Isolation
- Mid-isolation (shared servers, AD group permissions)
- High isolation (shared AD, dedicated everything else)
- You control the economic-risk slider
Costs
- Lowest cost per user
- Scale infrastructure and management efficiently
- Transparent cost models = informed customer choices
Security
- Inherently higher risk
- Mitigated by automation (e.g. Atria), strict permissions, segmentation
- Must be a clear risk vs economics discussion with the customer
Customization
- From branded wallpapers to dedicated app servers
- Customers lose direct AD admin—use your helpdesk or Atria instead
🔑 In Bullet Points
- One AD = less admin overhead
- One server farm = lower onboarding time/cost
- One consistent environment = easier helpdesk
- Share SQL, AV, Load Balancers
- Automate via scripts or Atria
- Multi-tenancy works even for complex orgs (like Government)%