· 10 min read
How ISVs Host Windows Applications at Scale: Multi-Tenant Design, Operations, and Automation
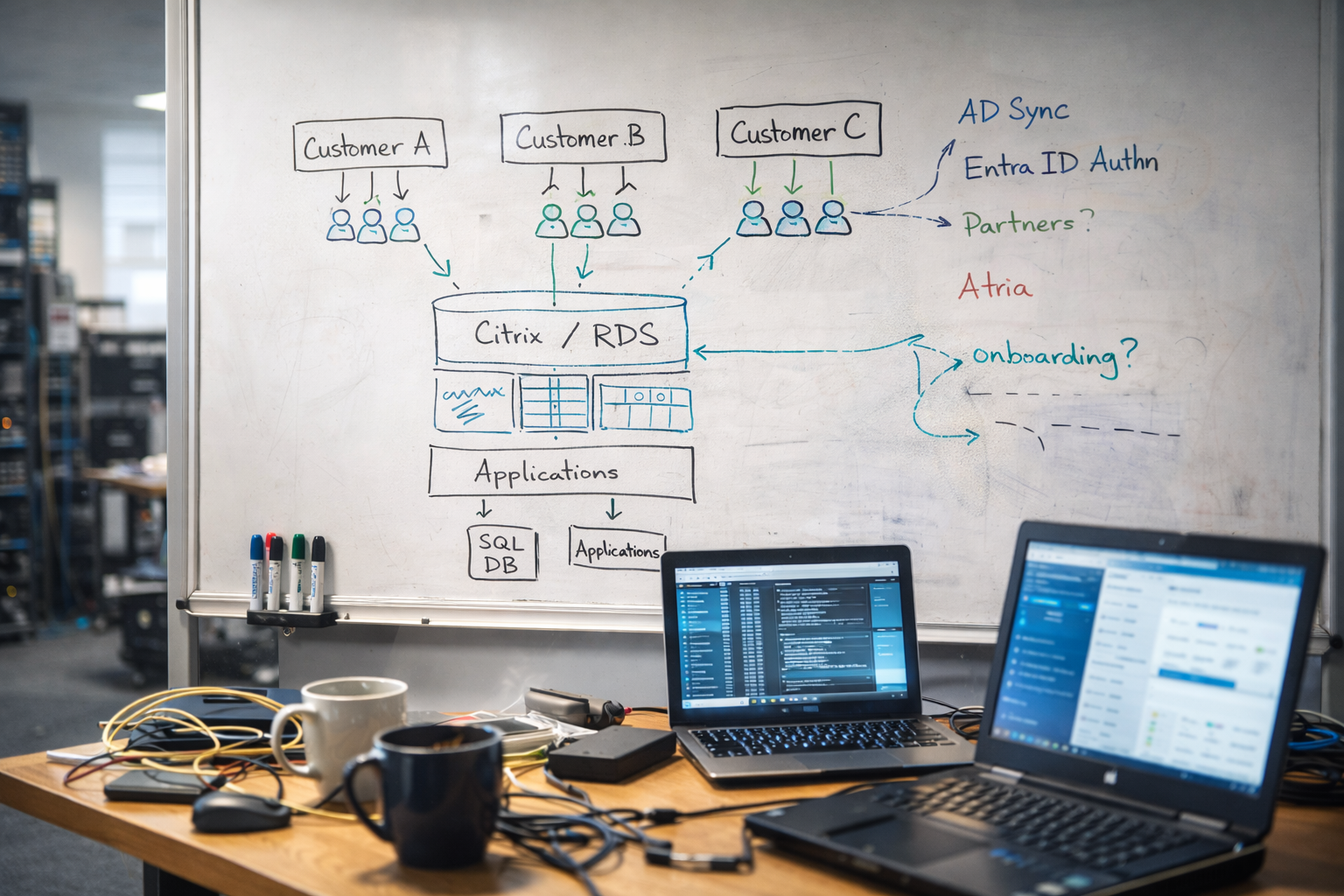
Hosting a Windows application with Citrix, RDS, or similar technology is only part of the problem. This guide explains how ISVs design multi-tenant platforms, where operations usually break down, and how automation helps platforms scale.
Many ISVs still depend on Windows applications that were built for line-of-business use, not for browser delivery. Those applications may be written in WinForms or WPF, rely on SQL Server, depend on Active Directory, or assume access to file shares and Windows-integrated authentication.
For many software vendors, rewriting that product into a true SaaS platform is a multi-year program with high commercial risk. Hosting the existing application is often the more practical path.
This article is for ISV leaders, platform architects, and operations teams who need to answer a very specific question:
How do you host a Windows application for many customers without turning onboarding, user management, and tenant administration into a permanent helpdesk problem?
The short answer is that application delivery technology solves only part of the challenge. The platform also needs a repeatable operational model for customers, users, permissions, databases, partners, and identity integration.
In practice, scaling hosted Windows applications usually requires:
- A delivery platform such as Citrix, RDS, Omnissa, Parallels RAS, or AVD
- A clear tenancy model across identity, storage, and application access
- Automation for onboarding, user lifecycle management, and delegated administration
- Operational guardrails that prevent customers, partners, and support teams from crossing tenant boundaries
- A management layer that reduces dependence on tickets, manual scripts, and privileged engineering effort
Why ISVs Still Choose Windows Application Hosting
Many vertical applications remain strongly tied to the Windows platform because they were designed around:
- Windows desktop user experiences
- SQL Server back ends
- Integrated authentication
- File-based workflows
- Mature but hard-to-replace business logic
Customers still want those applications delivered in a cloud-style model, but they may not need or want a full rewrite before they can modernise delivery.
That is why many ISVs continue to host Windows applications centrally and present them through technologies such as:
- Citrix
- Microsoft Remote Desktop Services (RDS)
- Omnissa Horizon
- Parallels RAS
- In some cases, Azure Virtual Desktop (AVD)
These platforms are good at delivering sessions, remote applications, and desktops. They can provide secure remote access and a strong user experience when the underlying application, profile design, storage, and network architecture are sound.
But that does not mean they solve the whole platform problem.
What the Delivery Platform Solves, and What It Does Not
Remote application platforms are primarily responsible for:
- Session brokering
- User connection workflows
- Remote display performance
- Policy and access controls at the delivery layer
- Desktop or application presentation
They do not usually solve the service-provider problems that appear when one platform supports many separate customers.
That second layer of work includes:
- Creating a new customer tenant
- Provisioning directory structures and access groups
- Creating or attaching SQL databases
- Applying file permissions
- Onboarding reseller or consulting partners
- Synchronising or federating identity
- Handling password resets and user lifecycle tasks
- Keeping customer boundaries intact
- Reporting on licence use and operational state
This is the point where many ISV platforms begin to struggle. The remote access layer may be working well, but the business is still running the service through tickets, scripts, and manual administration.
Where Hosted Windows Platforms Usually Break Down
When a hosted platform is small, manual operations can look manageable. As the customer count grows, the same weak points appear repeatedly.
1. User Management Turns Into a Helpdesk Queue
Creating users, modifying group membership, resetting passwords, enabling modules, and disabling leavers are routine tasks. In a shared platform, those tasks must also respect tenant boundaries and delegated administration rules.
If every request goes through the vendor helpdesk, support volume grows faster than the platform team expects.
2. Customer Onboarding Becomes Slow and Inconsistent
Onboarding a new customer often means coordinating several systems:
- Directory objects
- Security groups
- File storage
- Application configuration
- SQL databases
- Partner visibility
- Identity integration
If those steps are not standardised, every onboarding becomes a mini-project. That slows revenue recognition and introduces avoidable risk.
3. Partners Cannot Safely Support Their Own Customers
Many ISVs sell through consulting partners, resellers, or implementation specialists. Those partners often need to create users, manage customer access, or support onboarding.
Without delegated administration, the ISV helpdesk becomes a bottleneck for work that should be performed by the partner closest to the customer.
4. Tenant Isolation Relies on Human Discipline
This is one of the biggest risks in a growing platform. If customer boundaries depend on engineers remembering naming conventions or manually applying permissions, mistakes are inevitable.
Good platform design removes as much of that judgement as possible from day-to-day operations.
Windows Application Hosting Architecture Models
There is no single correct hosting model. The right design depends on the application, customer profile, support model, compliance requirements, and commercial goals.
Shared Directory Model
In a shared model, multiple customers are represented inside the same Active Directory environment. Separation is typically enforced through:
- Organisational units
- Security groups
- Delegated administration scopes
- Naming standards
- Application-level tenancy rules
This model can work well when the platform has strong operational discipline and the application is compatible with shared infrastructure.
Where it works well:
- Medium and high-volume platforms
- Customers with similar operational requirements
- Environments that need centralised administration efficiency
- Platforms where automation enforces repeatable tenant structure
Where it becomes risky:
- Poorly controlled delegation
- Inconsistent naming or group models
- Applications that assume broad directory visibility
- Customers with unusual policy or compliance requirements
Shared models are often economically attractive, but they demand a very mature operational design.
Dedicated Customer Environment Model
Some ISVs provide a private Active Directory or a more isolated stack for larger or more demanding customers.
This can make sense when a customer needs:
- Stronger isolation boundaries
- Custom group policy or security settings
- Unique integration patterns
- Dedicated SQL or application resources
- Contractual separation for governance reasons
Where it works well:
- Enterprise or regulated customers
- Premium service tiers
- Customers with special security or configuration needs
Trade-off:
Per-customer isolation usually reduces shared-platform efficiency. It can increase infrastructure count, operational effort, monitoring scope, and support complexity unless provisioning is heavily automated.
In practice, many mature platforms support both shared and dedicated patterns.
Designing the Operational Layer
The technical stack matters, but platform scale is usually determined by operational design rather than session delivery.
Tenant Provisioning
A new tenant often requires more than creating an OU or customer record. Typical steps include:
- Creating the customer container or tenant structure
- Applying baseline groups and roles
- Setting up storage locations and permissions
- Provisioning or mapping the customer database
- Enabling the correct application modules
- Establishing partner visibility rules
- Configuring identity sync or sign-in policy
If engineers perform those steps manually, the platform will slow down long before infrastructure capacity is exhausted.
User Lifecycle Management
User creation and change requests are deceptively expensive in large hosted environments. A mature operational model needs clear rules for:
- Who can create users
- Which attributes are mandatory
- Which groups map to which service tiers or modules
- How leavers are disabled
- How password reset responsibility is delegated
- How auditability is maintained
This is especially important when support teams, partners, and end-customer administrators all participate in user management.
Partner Delegation
Delegation needs to be intentional. A partner should be able to manage only:
- The customers assigned to that partner
- The users and services within their allowed scope
- The actions that match their role
That sounds obvious, but many platforms struggle here because partner access is bolted on after the platform is already in production.
Identity Integration
Customers increasingly want to use their own identity provider or maintain some connection to their internal directory.
Common options include:
- Provider-managed Active Directory accounts
- Synchronisation from the customer environment
- Entra ID-based sign-in for suitable applications and workflows
Each option changes the support model. Synchronisation introduces dependency on source-data quality. Federation introduces sign-in and trust dependencies. Shared platform identity introduces administrative overhead unless delegation is cleanly designed.
Delivery Platform Choice Still Matters
Citrix, RDS, Omnissa, Parallels RAS, and AVD are not interchangeable in every environment.
An ISV should evaluate them using criteria such as:
- Application compatibility
- User density and performance characteristics
- Profile and storage design
- Graphics or peripheral requirements
- Licensing model
- Operational tooling
- Customer location and latency
- Whether the platform is provider-operated, customer-operated, or hybrid
For example, AVD can be a strong fit in some scenarios, especially where Azure-native delivery is acceptable. But for some ISV-operated shared platforms, the operational model may be less straightforward than a centrally controlled service-provider environment. That is exactly why architecture decisions should be based on operating model, not just technology preference.
Common Mistakes ISVs Make
The same mistakes appear repeatedly in growing hosted platforms.
Treating Delivery as the Whole Solution
Buying a remote application platform does not create a scalable service model. It creates a delivery layer. The operational layer still has to be designed.
Building the First 20 Customers Manually
Manual onboarding and ticket-led administration often feel acceptable early on. Those habits become expensive technical debt once the platform is supporting hundreds of tenants.
Mixing Tenant Logic With Human Memory
If engineers must remember which groups, storage paths, or database templates belong to which customer type, consistency will break down.
Adding Partner Access as an Afterthought
Delegated administration should be designed early. Retro-fitting partner scope and self-service is usually harder than building it into the operating model from the start.
Ignoring the Economics of Support
A platform can be technically stable and still commercially weak if every user change, onboarding step, or customer update requires internal engineering time.
Where Atria Fits
Atria is not the remote application delivery platform. It is the management and automation layer that sits around the service-provider operating model.
In practice, that means Atria can help standardise and automate areas such as:
- Tenant creation
- User lifecycle workflows
- Delegated administration
- Partner-scoped management
- Directory-driven service management
- Customer visibility and control boundaries
That distinction matters. Citrix, RDS, Horizon, Parallels, or AVD may deliver the application session. Atria helps control the surrounding operational processes that determine whether the platform can scale efficiently.
It is also important to be clear about boundaries. A management layer does not remove the need for sound architecture, correct security design, application compatibility testing, or infrastructure capacity planning. Those still need to be designed properly.
A Practical Decision Framework
If you are designing or reviewing a hosted Windows application platform, these are the questions worth answering early:
- Will customers live in a shared identity model, dedicated environments, or a mix of both?
- Which user lifecycle tasks should stay with the ISV, and which should be delegated to partners or customers?
- How will tenant boundaries be enforced consistently across directory, storage, application, and database layers?
- What has to be automated before the platform reaches the next growth stage?
- Which parts of the operating model create the most support effort today?
- Which architecture decisions improve platform economics, and which simply move complexity elsewhere?
Those questions usually reveal whether the platform is truly designed to scale, or whether it is still relying on operational heroics.
Scaling Hosted Windows Applications
Hosting Windows applications is still a valid and often commercially smart strategy for ISVs. The hard part is not only delivering the application. It is designing a platform that can onboard customers quickly, manage users safely, support partners cleanly, and preserve tenant boundaries as the customer base grows.
The ISVs that do this well usually have three things in place:
- A delivery platform that fits the application
- A tenancy model with clear isolation rules
- An operational layer built around automation, delegation, and repeatable workflows
That is the problem Atria is built to help solve. Atria has been used by ISVs and hosting providers globally, from businesses building their first repeatable hosted model through to larger international providers operating multi-tenant platforms at significant scale.
If you want to see what that looks like in practice, explore our case studies:
- team.blue, which uses Atria to scale hosted services across European brands and reseller channels
- Visory, which uses Atria to automate high-volume QuickBooks hosting in a multi-tenant Active Directory and Citrix environment
If you want to go deeper on how Atria supports these environments, see our ISV automation platform page and our Active Directory management capabilities.
Those examples show the same underlying pattern: delivery technology matters, but scale comes from getting the operating model right.